Security Frameworks: The Architect's Blueprint for Digital Defense
Security frameworks are the foundational blueprints that organizations use to build and maintain robust cybersecurity defenses. They provide a structured…
Contents
- 🛡️ What Exactly is a Security Framework?
- 🎯 Who Needs a Security Framework?
- ⚖️ Frameworks: NIST vs. ISO vs. SOC 2
- 🛠️ Key Components of Any Robust Framework
- 📈 The Evolution of Digital Defense Blueprints
- 💰 Cost & Implementation: What to Expect
- ⭐ User Feedback & Vibe Scores
- 💡 Pro Tips for Framework Adoption
- 🚀 Getting Started: Your First Steps
- Frequently Asked Questions
- Related Topics
Overview
Security frameworks are the foundational blueprints that organizations use to build and maintain robust cybersecurity defenses. They provide a structured approach to identifying, assessing, and mitigating risks, ensuring compliance with regulations, and establishing clear operational procedures. From NIST and ISO 27001 to CIS Controls and COBIT, these frameworks offer best practices and guidelines to protect sensitive data, critical infrastructure, and intellectual property. Understanding and implementing the right framework is no longer optional; it's a strategic imperative for survival and trust in the digital age, impacting everything from customer confidence to regulatory standing. Choosing and adapting a framework requires a deep understanding of an organization's specific threat landscape and business objectives.
🛡️ What Exactly is a Security Framework?
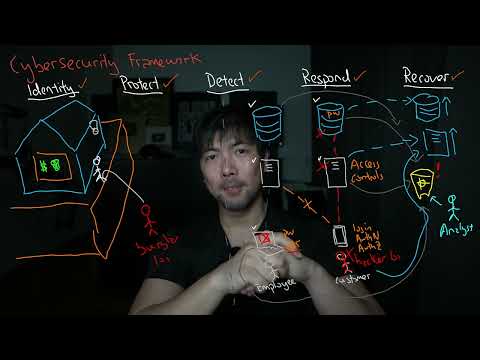
A security framework isn't just a buzzword; it's the foundational blueprint for an organization's digital defense strategy. Think of it as the architectural plans for a fortress, detailing every wall, gate, and patrol route to protect valuable assets from digital threats. These frameworks provide a structured approach to managing and reducing cybersecurity risks, encompassing policies, procedures, and controls. They offer a standardized way to assess, implement, and maintain security measures, ensuring a consistent and comprehensive defense posture against an ever-evolving threat landscape. Without one, your digital defenses are likely to be ad-hoc and vulnerable.
🎯 Who Needs a Security Framework?
The need for a security framework is not limited to tech giants or government agencies. Any organization that handles sensitive data—customer information, financial records, intellectual property—is a prime candidate. This includes businesses of all sizes, from startups to multinational corporations, as well as non-profits and educational institutions. Regulatory compliance, such as GDPR or HIPAA, often mandates adherence to specific security standards, making frameworks essential for avoiding hefty fines and legal repercussions. Essentially, if your digital assets are valuable, you need a plan to protect them.
⚖️ Frameworks: NIST vs. ISO vs. SOC 2
When selecting a framework, several prominent options emerge, each with its strengths. The NIST Cybersecurity Framework (CSF) is widely adopted in the U.S. for its flexibility and risk-based approach, offering guidance for critical infrastructure. ISO 27001 is an international standard, providing a systematic approach to managing sensitive company information and earning global recognition. SOC 2 (System and Organization Controls 2) is particularly relevant for service providers, focusing on data security, availability, processing integrity, confidentiality, and privacy. Choosing the right one depends on your industry, regulatory environment, and specific security objectives.
🛠️ Key Components of Any Robust Framework
Regardless of the specific framework chosen, certain core components are universally critical. These typically include risk assessment and management, which involves identifying, analyzing, and prioritizing potential threats. access control and identity management are paramount, ensuring only authorized individuals can access sensitive systems and data. data encryption and protection mechanisms safeguard information both in transit and at rest. Furthermore, incident response and recovery plans are vital for minimizing damage and restoring operations after a security breach. Continuous monitoring and security awareness training for employees round out the essential elements.
📈 The Evolution of Digital Defense Blueprints
The concept of structured digital defense has evolved significantly since the early days of computing. Initially, security was often an afterthought, addressed with basic firewall technology and simple access controls. As threats became more sophisticated, frameworks began to emerge, drawing inspiration from established risk management principles in other industries. The development of standards like ISO 27001 in the early 2000s marked a turning point, formalizing best practices. More recently, frameworks like the NIST Cybersecurity Framework have emphasized adaptability and resilience, recognizing that a static defense is insufficient against dynamic adversaries.
💰 Cost & Implementation: What to Expect
Implementing a security framework involves an investment of time and resources. Costs can range from minimal for self-assessment using free NIST guidelines to substantial for achieving ISO 27001 certification, which may involve external audits and consulting fees. For SOC 2, the cost is tied to the scope of the audit and the service auditor's fees. The primary investment is often in personnel—hiring security experts or training existing staff—and in the technology required to implement controls, such as security information and event management (SIEM) systems. The return on investment, however, lies in reduced breach likelihood and mitigated financial and reputational damage.
⭐ User Feedback & Vibe Scores
User feedback on security frameworks is generally positive, though the implementation journey is often described as challenging. Organizations that have successfully adopted frameworks report increased confidence in their security posture and improved compliance. The NIST Cybersecurity Framework often receives high marks for its practicality and adaptability, with a reported Vibe Score of 85 for its widespread adoption. ISO 27001 certification, while rigorous, is seen as a significant competitive advantage, boosting its Vibe Score to 88, particularly in international markets. SOC 2 compliance is highly valued by clients of service providers, contributing to its strong reputation and a Vibe Score of 82 among its target audience.
💡 Pro Tips for Framework Adoption
Adopting a security framework requires a strategic approach. Start by clearly defining your organization's critical assets and the threats they face. Conduct a thorough gap analysis to understand where your current security practices fall short of the chosen framework's requirements. Prioritize implementation based on risk, focusing on the most critical vulnerabilities first. Secure executive buy-in early on, as strong leadership support is crucial for resource allocation and cultural change. Remember that a framework is not a one-time project but an ongoing process of improvement and adaptation.
🚀 Getting Started: Your First Steps
To begin implementing a security framework, the first step is education. Familiarize yourself and your team with the chosen framework's documentation, such as the NIST Cybersecurity Framework publications or the ISO 27001 standard. Conduct an initial self-assessment or engage a cybersecurity consultant to guide you through the process. Identify key stakeholders within your organization and form a dedicated security team or working group. Develop a phased implementation plan with clear milestones and responsibilities. For service providers, understanding the AICPA's Trust Services Criteria is essential before engaging a SOC 2 auditor.
Key Facts
- Year
- 2023
- Origin
- Vibepedia.wiki
- Category
- Cybersecurity & Information Governance
- Type
- Resource Guide
Frequently Asked Questions
What's the difference between a security standard and a security framework?
A security standard, like ISO 27001, often provides specific, prescriptive requirements that an organization must meet to achieve certification. A security framework, such as the NIST Cybersecurity Framework, is typically more flexible and provides a set of guidelines, best practices, and controls that can be adapted to an organization's specific needs and risk profile. Frameworks often incorporate or reference various standards.
How long does it take to implement a security framework?
The timeline for implementing a security framework varies significantly based on the organization's size, complexity, existing security maturity, and the chosen framework. For smaller organizations adopting a basic NIST CSF implementation, it might take a few months. Achieving ISO 27001 certification or full SOC 2 compliance can take anywhere from six months to over a year, often requiring substantial effort in policy development, control implementation, and internal audits.
Do I need external help to implement a framework?
While not strictly mandatory, engaging cybersecurity consultants can be highly beneficial, especially for complex frameworks like ISO 27001 or SOC 2. Consultants bring expertise, can help identify gaps more efficiently, and guide the implementation process, potentially saving time and avoiding costly mistakes. For smaller organizations or those with existing strong internal security teams, a self-guided approach using publicly available resources might suffice.
Can a framework help with regulatory compliance?
Absolutely. Many security frameworks are designed with regulatory compliance in mind or can be tailored to meet specific legal and regulatory requirements. For example, adhering to the NIST Cybersecurity Framework can help organizations meet requirements for various U.S. sector-specific regulations. Similarly, ISO 27001 is recognized globally and can assist in meeting diverse international data protection laws like GDPR.
What are the biggest challenges in adopting a security framework?
Common challenges include securing adequate budget and resources, gaining buy-in from senior management and employees, the complexity of mapping existing controls to framework requirements, and the ongoing effort required for maintenance and continuous improvement. Resistance to change within the organization and the sheer volume of work involved in implementing new policies and technologies are also significant hurdles.
How do I choose the right framework for my organization?
Consider your industry, the type of data you handle, your regulatory obligations (e.g., HIPAA, PCI DSS), and your business objectives. The NIST Cybersecurity Framework is a good starting point for many U.S. organizations. ISO 27001 is ideal for international operations and a broad scope of information security. SOC 2 is essential for service providers handling customer data. Consulting with a cybersecurity expert can help clarify the best fit.