AES Algorithm | Vibepedia
The Advanced Encryption Standard (AES) is the de facto global benchmark for symmetric-key encryption, a cryptographic algorithm that secures everything from…
Contents
- 🎵 Origins & History
- ⚙️ How It Works
- 📊 Key Facts & Numbers
- 👥 Key People & Organizations
- 🌍 Cultural Impact & Influence
- ⚡ Current State & Latest Developments
- 🤔 Controversies & Debates
- 🔮 Future Outlook & Predictions
- 💡 Practical Applications
- 📚 Related Topics & Deeper Reading
- Frequently Asked Questions
- References
- Related Topics
Overview
The Advanced Encryption Standard (AES) is the de facto global benchmark for symmetric-key encryption, a cryptographic algorithm that secures everything from sensitive government communications to your everyday online banking. Born from a competition initiated by the U.S. National Institute of Standards and Technology (NIST) in 1997, AES was officially adopted in 2001, replacing the aging Data Encryption Standard (DES). Its strength lies in its mathematical elegance and robust security, offering key lengths of 128, 192, or 256 bits, all operating on a fixed 128-bit block size. Developed by Belgian cryptographers Joan Daemen and Vincent Rijmen under the name Rijndael, AES is renowned for its efficiency and resistance to known cryptanalytic attacks, making it a cornerstone of cybersecurity for governments, businesses, and individuals worldwide.
🎵 Origins & History
The genesis of the AES Algorithm traces back to the late 1990s when the U.S. National Institute of Standards and Technology (NIST) recognized the critical need to replace the vulnerable Data Encryption Standard (DES). In 1997, NIST launched a global competition to find a successor, inviting cryptographers worldwide to submit their best designs. From a field of 15 submissions, a Belgian-developed cipher named Rijndael, created by Joan Daemen and Vincent Rijmen, emerged as the frontrunner. After rigorous analysis and refinement, NIST officially selected Rijndael as the AES in October 2000, publishing the standard as FIPS PUB 197 in 2001. This marked a pivotal moment, establishing a new global cryptographic standard that would underpin digital security for decades to come.
⚙️ How It Works
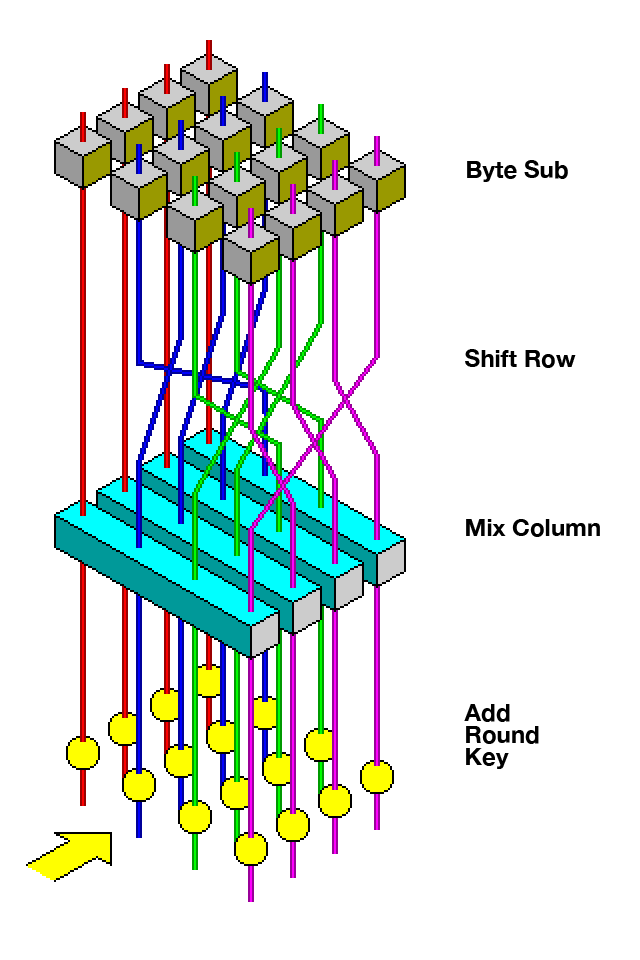
At its core, the AES Algorithm is a symmetric-key block cipher. It operates by dividing plaintext into fixed-size blocks of 128 bits. The encryption process involves a series of transformations—substitution, permutation, and mixing—applied iteratively over multiple rounds. The number of rounds depends on the key length: 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys. Each round uses a unique round key derived from the original secret key through a process called key expansion. Decryption reverses these steps using the same secret key, ensuring that only authorized parties with the key can access the original data. This iterative, key-dependent transformation makes brute-force attacks computationally infeasible with current technology.
📊 Key Facts & Numbers
The AES Algorithm is defined with a standard block size of 128 bits, but supports three distinct key lengths: 128, 192, and 256 bits. NIST's initial selection focused on these three variants, offering a spectrum of security versus performance. For instance, AES-128 requires approximately 10 rounds, while AES-256 necessitates 14 rounds, impacting processing speed. The algorithm has been implemented in countless hardware and software solutions, with performance benchmarks showing speeds ranging from tens of megabytes per second on low-power embedded systems to gigabytes per second on high-performance processors. As of 2024, no practical attacks have been demonstrated against AES with key lengths of 128 bits or higher, solidifying its position as a highly secure standard.
👥 Key People & Organizations
The development and standardization of the AES Algorithm involved key individuals and organizations. The primary architects of the Rijndael cipher were Belgian cryptographers Joan Daemen and Vincent Rijmen, whose innovative design won the NIST competition. The National Institute of Standards and Technology (NIST), a U.S. government agency, spearheaded the selection process and published the official standard (FIPS PUB 197). Leading cybersecurity firms and academic institutions worldwide, including IBM and Intel, have played crucial roles in implementing and optimizing AES for various platforms, ensuring its widespread adoption and continued security.
🌍 Cultural Impact & Influence
The AES Algorithm has profoundly shaped the landscape of digital security, becoming the gold standard for encrypting sensitive information across the globe. Its adoption by governments, financial institutions, and technology companies has made it ubiquitous in securing everything from classified documents and online transactions to Wi-Fi networks and mobile communications. The widespread implementation of AES has fostered trust in digital systems and enabled the growth of e-commerce and cloud computing. Its influence is evident in countless security protocols, including TLS/SSL, IPsec, and SSH, which rely on AES for confidentiality and integrity.
⚡ Current State & Latest Developments
As of 2024, the AES Algorithm remains the dominant symmetric encryption standard. While no practical attacks have broken AES-128, AES-192, or AES-256, ongoing research continues to explore theoretical vulnerabilities, particularly in the context of potential future quantum computing capabilities. NIST has initiated efforts to standardize post-quantum cryptography, but AES is expected to remain a critical component of hybrid cryptographic solutions for the foreseeable future. Companies like Apple and Google continue to integrate AES into their operating systems and hardware, such as Apple's T2 Security Chip and Google Pixel phones, for full-disk encryption and secure data storage.
🤔 Controversies & Debates
While the AES Algorithm is widely regarded as secure, debates persist regarding its long-term viability, especially against emerging threats like quantum computing. Some researchers argue that AES-256 might eventually be necessary to provide sufficient security margins against future cryptanalytic advancements, while others emphasize that current implementations are robust. A persistent controversy revolves around the potential for side-channel attacks, which exploit physical characteristics of the computing device (like power consumption or timing) rather than mathematical weaknesses in the algorithm itself. Ensuring secure implementation of AES, free from such vulnerabilities, remains a critical challenge for developers and security professionals.
🔮 Future Outlook & Predictions
The future of the AES Algorithm is intrinsically linked to the evolution of computing power and cryptographic research. While AES is expected to remain secure against classical computers for the foreseeable future, the advent of large-scale quantum computers poses a theoretical threat. Cryptographers are actively developing post-quantum cryptographic algorithms designed to resist quantum attacks. It is likely that AES will be used in conjunction with these new algorithms in a hybrid approach to ensure continued security. NIST's ongoing standardization process for post-quantum cryptography, expected to finalize in the coming years, will dictate the transition path, but AES's efficiency and proven track record suggest it will persist in some capacity for many years.
💡 Practical Applications
The AES Algorithm is deployed in an astonishing array of practical applications, forming the backbone of modern digital security. It is used for full-disk encryption on operating systems like Windows (BitLocker) and macOS (FileVault), protecting user data at rest. In network security, AES is integral to protocols like TLS/SSL (securing HTTPS websites), IPsec (for VPNs), and Wi-Fi Protected Access (WPA2/WPA3). It also secures communication channels in messaging apps, encrypts data stored in cloud services like AWS and Azure, and is embedded in hardware security modules (HSMs) for protecting cryptographic keys.
Key Facts
- Year
- 2001
- Origin
- Belgium / United States
- Category
- technology
- Type
- technology
Frequently Asked Questions
What is the AES algorithm and why is it important?
The AES Algorithm is a symmetric-key encryption standard adopted by the U.S. government and widely used globally. It's crucial because it provides a robust and efficient method for protecting sensitive digital information, from government secrets to personal data, ensuring confidentiality and integrity. Its widespread adoption makes it a foundational element of modern cybersecurity, underpinning secure communications and data storage across numerous applications and protocols.
How does AES encryption work at a high level?
AES works by taking plaintext data, dividing it into 128-bit blocks, and then applying a series of mathematical transformations—substitution, permutation, and mixing—over multiple rounds. Each round uses a unique key derived from the original secret key. The number of rounds depends on the key length (10 for 128-bit, 12 for 192-bit, 14 for 256-bit). Decryption reverses these steps using the same secret key, making it computationally infeasible for unauthorized parties to decipher the data without knowing the key.
What are the different key lengths for AES and what's the difference?
The AES Algorithm supports three key lengths: 128 bits, 192 bits, and 256 bits. The primary difference lies in the number of encryption rounds performed: 10 rounds for AES-128, 12 for AES-192, and 14 for AES-256. Longer key lengths offer greater theoretical security against brute-force attacks but require more computational resources, potentially slowing down encryption and decryption processes. For most applications, AES-128 provides an excellent balance of security and performance.
Has AES ever been broken?
To date, there are no known practical attacks that can break the AES Algorithm with its standard key lengths (128, 192, or 256 bits) using classical computing methods. While theoretical vulnerabilities and attacks exploiting implementation flaws (like side-channel attacks) have been studied, the core algorithm remains secure. Cryptographers continue to research its resilience, especially in light of potential future quantum computing advancements, but AES is still considered the gold standard for symmetric encryption.
What is the difference between AES and DES?
The AES Algorithm is the successor to the Data Encryption Standard (DES). DES, developed in the 1970s, uses a 56-bit key and a 64-bit block size, making it vulnerable to brute-force attacks with modern computing power. AES, on the other hand, uses significantly longer keys (128, 192, or 256 bits) and a 128-bit block size, offering vastly superior security and efficiency. NIST standardized AES in 2001 to replace the outdated and compromised DES.
Where is AES used in everyday technology?
You encounter the AES Algorithm constantly. It's used for full-disk encryption on your computer (like Windows BitLocker or macOS FileVault), securing your Wi-Fi network (WPA2/WPA3), encrypting communications for websites (HTTPS via TLS/SSL), and protecting data in cloud storage services like AWS. Many secure messaging apps and VPN services also rely on AES for end-to-end encryption.
What is the future of AES encryption?
The AES Algorithm is expected to remain a vital part of cybersecurity for years to come, particularly against classical computing threats. However, the rise of quantum computing presents a theoretical challenge. NIST is standardizing post-quantum cryptographic algorithms, and future systems may employ a hybrid approach combining AES with these new methods. While AES's role might evolve, its efficiency and proven security ensure its continued relevance in the foreseeable future.