Advanced Encryption Standard (AES) | Vibepedia
The Advanced Encryption Standard (AES), originally known as Rijndael, is the de facto global benchmark for symmetric-key encryption. Established by the U.S…
Contents
- 🎵 Origins & History
- ⚙️ How It Works
- 📊 Key Facts & Numbers
- 👥 Key People & Organizations
- 🌍 Cultural Impact & Influence
- ⚡ Current State & Latest Developments
- 🤔 Controversies & Debates
- 🔮 Future Outlook & Predictions
- 💡 Practical Applications
- 📚 Related Topics & Deeper Reading
- Frequently Asked Questions
- References
- Related Topics
Overview
The genesis of the Advanced Encryption Standard (AES) can be traced back to 1997 when NIST initiated a public competition to find a successor for the Data Encryption Standard (DES), which was showing vulnerabilities against brute-force attacks. The winning algorithm, Rijndael, was developed by Belgian cryptographers Joan Daemen and Vincent Rijmen of COSIC Group at the Katholieke Universiteit Leuven. Their proposal, submitted in 1998, was chosen after a rigorous evaluation process involving cryptographers worldwide. NIST officially adopted Rijndael as AES in October 2001, publishing it as Federal Information Processing Standard (FIPS) Publication 197. This marked a significant shift towards a more secure and modern encryption standard, moving away from the older DES algorithm that had been in use since 1977.
⚙️ How It Works
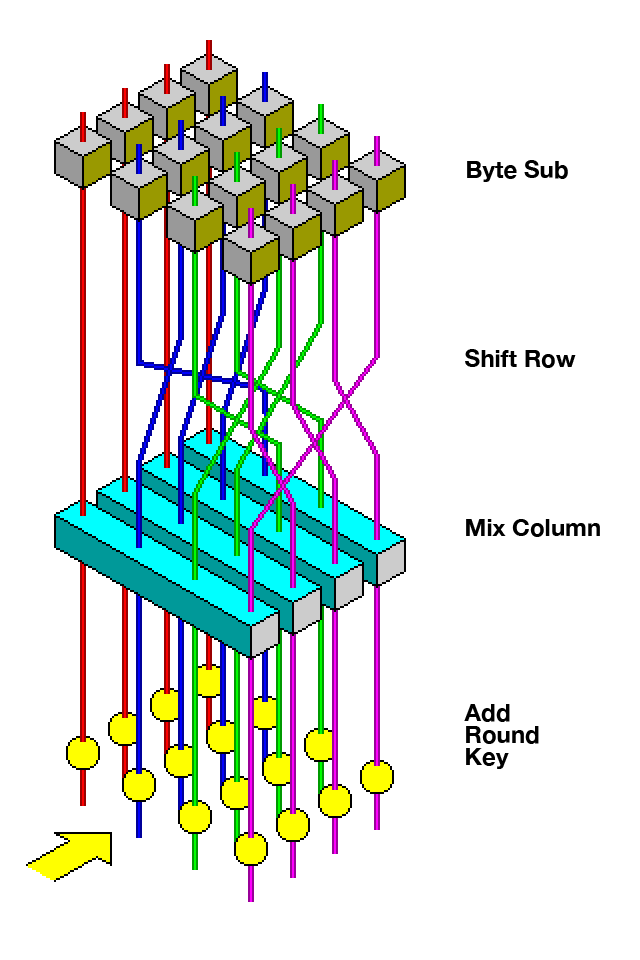
AES is a block cipher, meaning it encrypts data in fixed-size chunks, specifically 128-bit blocks. It employs a substitution-permutation network design, which involves multiple rounds of transformations. Each round consists of four distinct operations: AddRoundKey, SubBytes, ShiftRows, and MixColumns. The number of rounds depends on the key length: 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys. The AddRoundKey step combines the current block with a round key derived from the main AES key schedule. This iterative process, combined with the key expansion, ensures that even small changes in the plaintext or key result in drastically different ciphertexts, a property known as avalanche effect.
📊 Key Facts & Numbers
AES operates on 128-bit blocks, meaning it can encrypt approximately 16 bytes of data at a time. The standard supports three key lengths: 128 bits (16 bytes), 192 bits (24 bytes), and 256 bits (32 bytes). A 128-bit AES key offers 2^128 possible combinations, a number so vast that it would take the most powerful supercomputers billions of years to brute-force. NIST estimates that encrypting the entire world's data with AES-128 would require approximately 3.2 x 10^30 years. As of 2024, AES-256 is considered the gold standard for high-security applications, providing a theoretical security margin of 2^256 operations. The algorithm's computational efficiency allows it to be implemented on devices with limited processing power, including smart cards and embedded systems.
👥 Key People & Organizations
The primary architects of AES are Joan Daemen and Vincent Rijmen, whose Rijndael cipher formed the basis of the standard. The NIST played a pivotal role in selecting and standardizing AES, with key figures like Ray Johnson overseeing the selection process. Major technology companies such as Microsoft, Apple, and Google have integrated AES into their operating systems and products, contributing to its widespread deployment. Security organizations like the European Union Agency for Cybersecurity (ENISA) and the U.S. National Security Agency (NSA) have also endorsed and utilized AES for protecting sensitive data.
🌍 Cultural Impact & Influence
AES has become the invisible backbone of digital security, profoundly influencing how data is protected across the globe. Its adoption by governments, including the U.S. government, for protecting classified information has lent it immense credibility. Major software platforms like Microsoft Windows and macOS utilize AES for full-disk encryption, safeguarding user data. The proliferation of SSL/TLS certificates, which secure web traffic, heavily relies on AES for encrypting communications between browsers and servers. Its presence in Wi-Fi security protocols like WPA2 and WPA3 has made secure wireless networking a reality for billions. The cultural impact is subtle but pervasive; AES ensures the privacy of online banking, secure messaging apps like Signal, and cloud storage services.
⚡ Current State & Latest Developments
As of 2024, AES remains the dominant symmetric encryption algorithm. While no practical attacks have been found against full AES (128, 192, or 256-bit keys) in real-world scenarios, cryptographers continue to explore theoretical vulnerabilities. NIST periodically reviews cryptographic standards, and while AES is not currently slated for replacement, research into post-quantum cryptography is ongoing, which may eventually lead to new standards that are resistant to quantum computing attacks. Implementations are constantly being optimized for performance and security on various platforms, from IoT devices to high-performance computing clusters. The ongoing development of side-channel attack countermeasures also represents a significant area of current work.
🤔 Controversies & Debates
The primary debate surrounding AES centers on its theoretical security against future computational advancements, particularly quantum computing. While classical computers are unlikely to break AES-128 or AES-256 in any feasible timeframe, quantum computers, if realized at scale, could potentially reduce the effective key length. For instance, Grover's algorithm could theoretically speed up brute-force attacks, making AES-128 as vulnerable as a 64-bit key to a quantum attacker. This has spurred research into post-quantum cryptography (PQC) algorithms. Another area of discussion involves side-channel attacks, where information is leaked through physical means like power consumption or timing, though these are implementation-specific rather than flaws in the core AES algorithm itself. The NSA's recommendation of AES-256 for top-secret information highlights the ongoing trust in its strength.
🔮 Future Outlook & Predictions
The future of AES is intrinsically linked to the evolution of computing power and the threat landscape. While AES is expected to remain a cornerstone of symmetric encryption for the foreseeable future, its long-term dominance may be challenged by the advent of large-scale quantum computers. NIST's PQC standardization process, aiming to select new algorithms resistant to quantum attacks, is a critical development. It's plausible that AES will coexist with PQC algorithms, with AES used for classical computing environments and PQC for quantum-resistant applications. Furthermore, advancements in hardware acceleration for AES and the development of more sophisticated side-channel attack mitigation techniques will continue to shape its practical deployment. The ongoing arms race between cryptographers and attackers ensures that AES, like all cryptographic standards, will be subject to continuous scrutiny and potential evolution.
💡 Practical Applications
AES is ubiquitous in modern technology, serving as the encryption engine for a vast array of applications. It's used in full-disk encryption solutions like BitLocker on Windows and FileVault on macOS to protect data at rest. For data in transit, AES is fundamental to securing internet communications via SSL/TLS protocols, protecting everything from web browsing to VPN connections. It's also integral to wireless security standards like WPA2 and WPA3, securing Wi-Fi networks. Many file compression and archiving tools, such as 7-Zip and WinRAR, offer AES encryption for secure file transfer. Furthermore, it's employed in secure messaging applications, database encryption, and hardware security modules (HSMs) for protecting cryptographic keys.
Key Facts
- Year
- 2001
- Origin
- Belgium / United States
- Category
- technology
- Type
- technology
Frequently Asked Questions
Is AES truly unbreakable?
For all practical purposes on classical computers, AES is considered unbreakable. The computational power required to brute-force AES-128 or AES-256 is astronomically high, far exceeding current and foreseeable capabilities. However, theoretical attacks, particularly those leveraging quantum computing like Grover's algorithm, could potentially reduce the effective security. Cryptographers continue to research and develop post-quantum cryptography to address future threats.
What's the difference between AES-128, AES-192, and AES-256?
The numbers refer to the key length in bits. AES-128 uses a 128-bit key, AES-192 uses a 192-bit key, and AES-256 uses a 256-bit key. A longer key generally provides a higher level of security against brute-force attacks because there are more possible keys to try. For instance, AES-256 offers 2^256 possible keys, compared to 2^128 for AES-128. The U.S. National Security Agency (NSA) recommends AES-256 for protecting information classified as Top Secret.
Why was AES chosen over other encryption algorithms?
AES was selected through a rigorous, open competition run by NIST. The Rijndael algorithm, which became AES, was chosen for its strong security, excellent performance across a wide range of hardware and software platforms, and its efficient implementation. It offered a good balance of security and speed, surpassing many other candidates in these critical areas. Its design was also considered elegant and well-understood by the cryptographic community.
Where is AES used in everyday technology?
AES is used everywhere. When you browse a website securely (look for the padlock icon and 'https'), AES is likely encrypting your connection via SSL/TLS. Your smartphone's data is protected by AES through full-disk encryption features like FileVault on Apple devices or BitLocker on Windows. Secure Wi-Fi networks use AES via WPA2 or WPA3. Many file archiving tools like 7-Zip also offer AES encryption for securing files.
Can quantum computers break AES?
Theoretically, yes, but not easily. Quantum computers, if built at a sufficient scale, could use algorithms like Grover's algorithm to speed up brute-force key searches. This would effectively halve the security strength of AES keys. For example, AES-128 might become as vulnerable as a 64-bit key. This is why NIST is actively standardizing post-quantum cryptography algorithms designed to resist quantum attacks, though AES is still considered secure against current classical computers.
How do I encrypt my files using AES?
Many operating systems and third-party applications offer AES encryption. On Windows, BitLocker can encrypt your entire drive. For individual files, tools like 7-Zip (free) or WinRAR allow you to create password-protected archives using AES-256 encryption. macOS users can use Disk Utility to create encrypted disk images or FileVault for full-disk encryption. Ensure you use a strong, unique password for your encryption, as losing it means losing access to your data.
What are the main security concerns with AES implementations?
While the AES algorithm itself is exceptionally secure, implementations can be vulnerable. Side-channel attacks exploit physical leakage, such as power consumption or electromagnetic radiation, to infer secret keys. Poorly designed key management practices, such as storing keys insecurely or using weak passwords, are also significant risks. Ensuring that AES is implemented correctly, with robust key management and protections against side-channel leakage, is crucial for maintaining its security in practice.